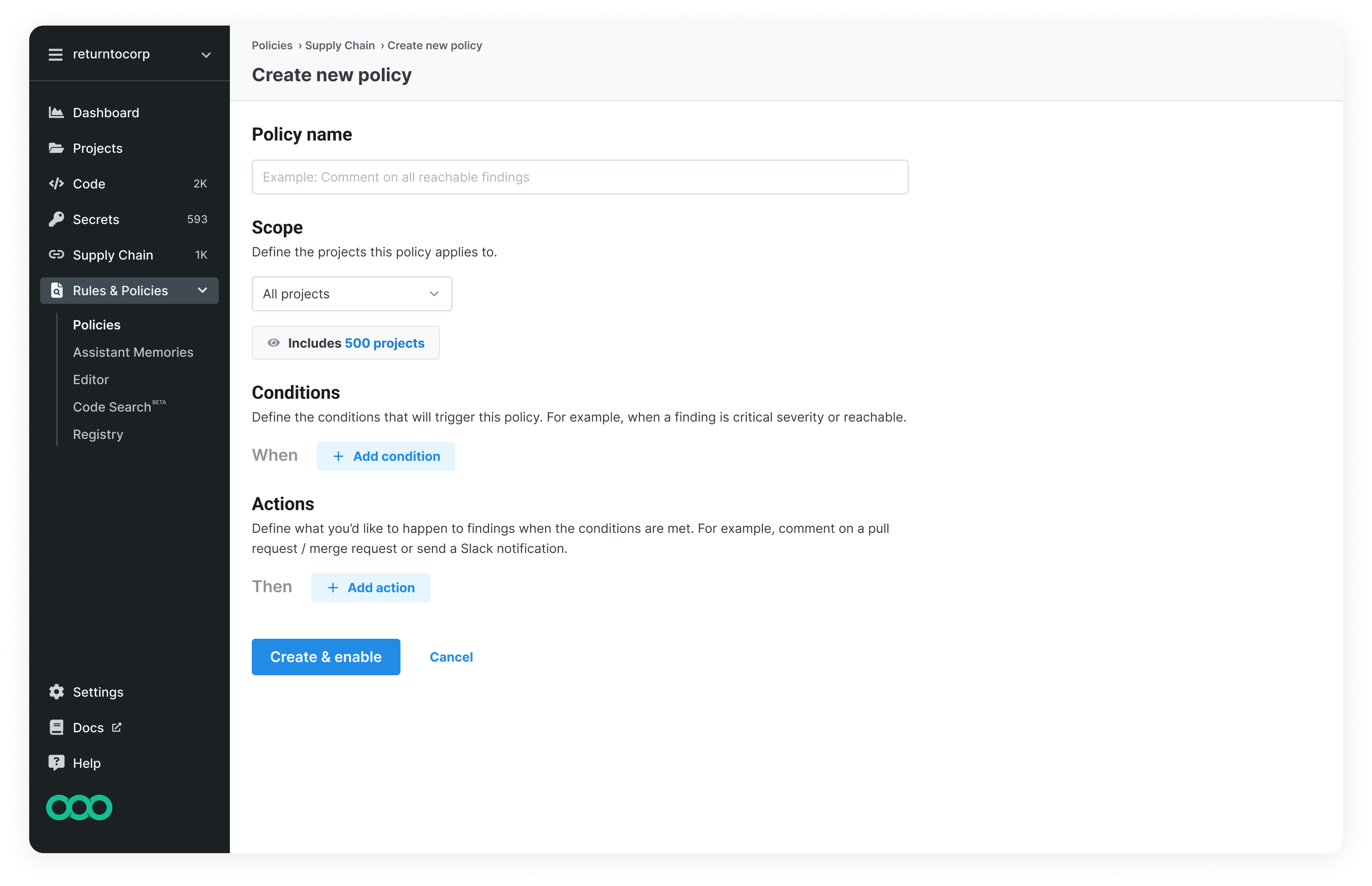
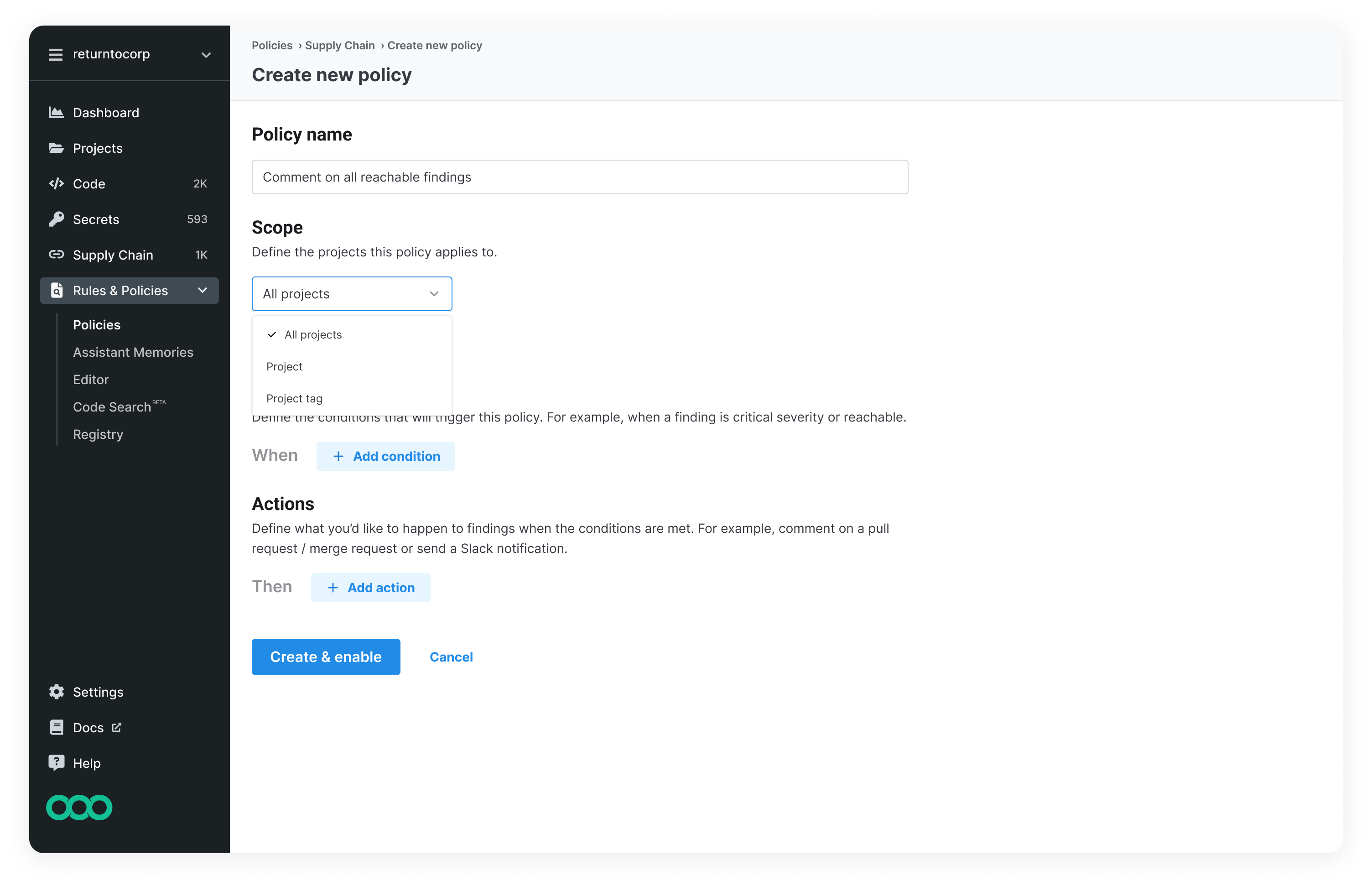
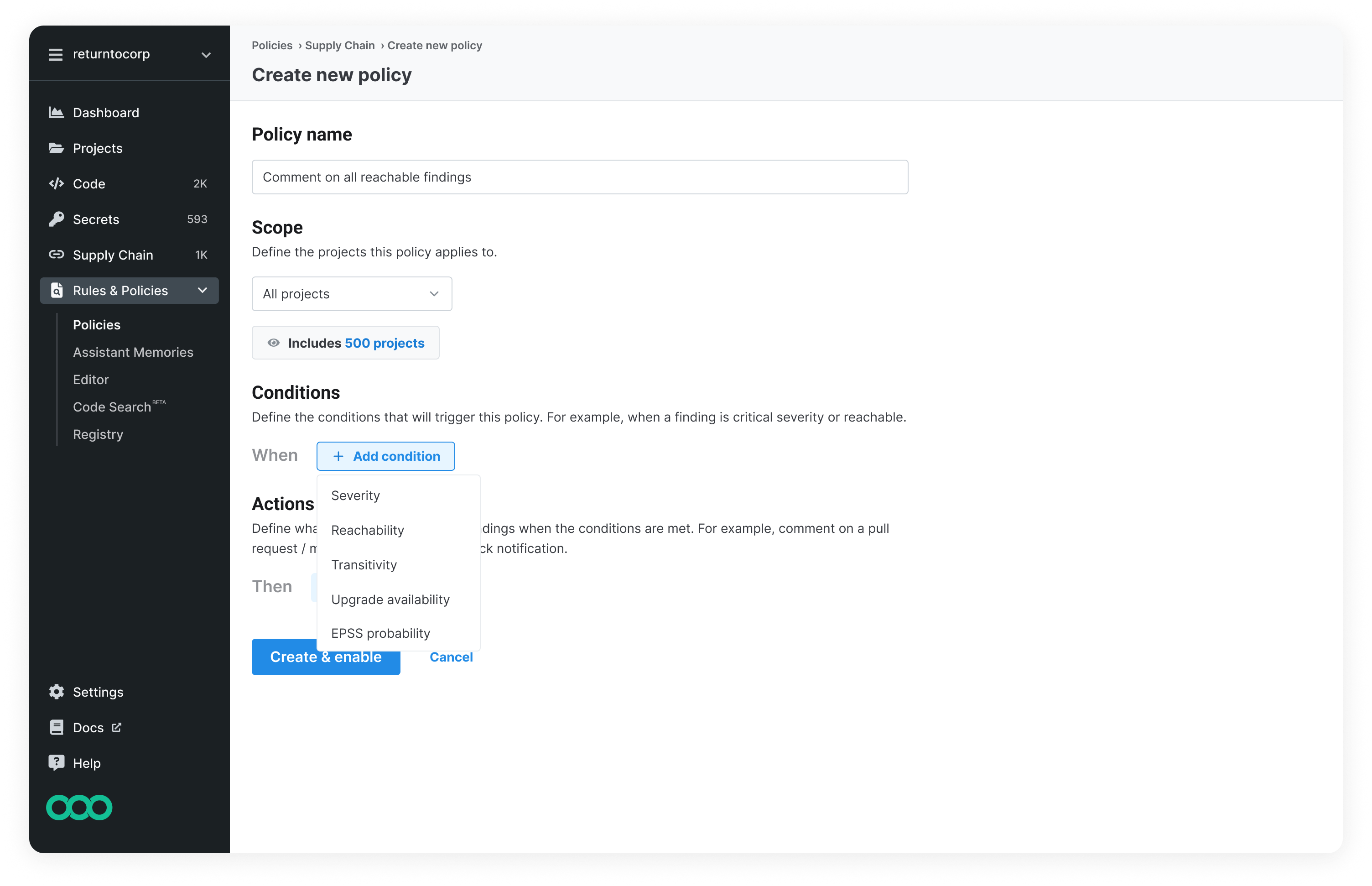
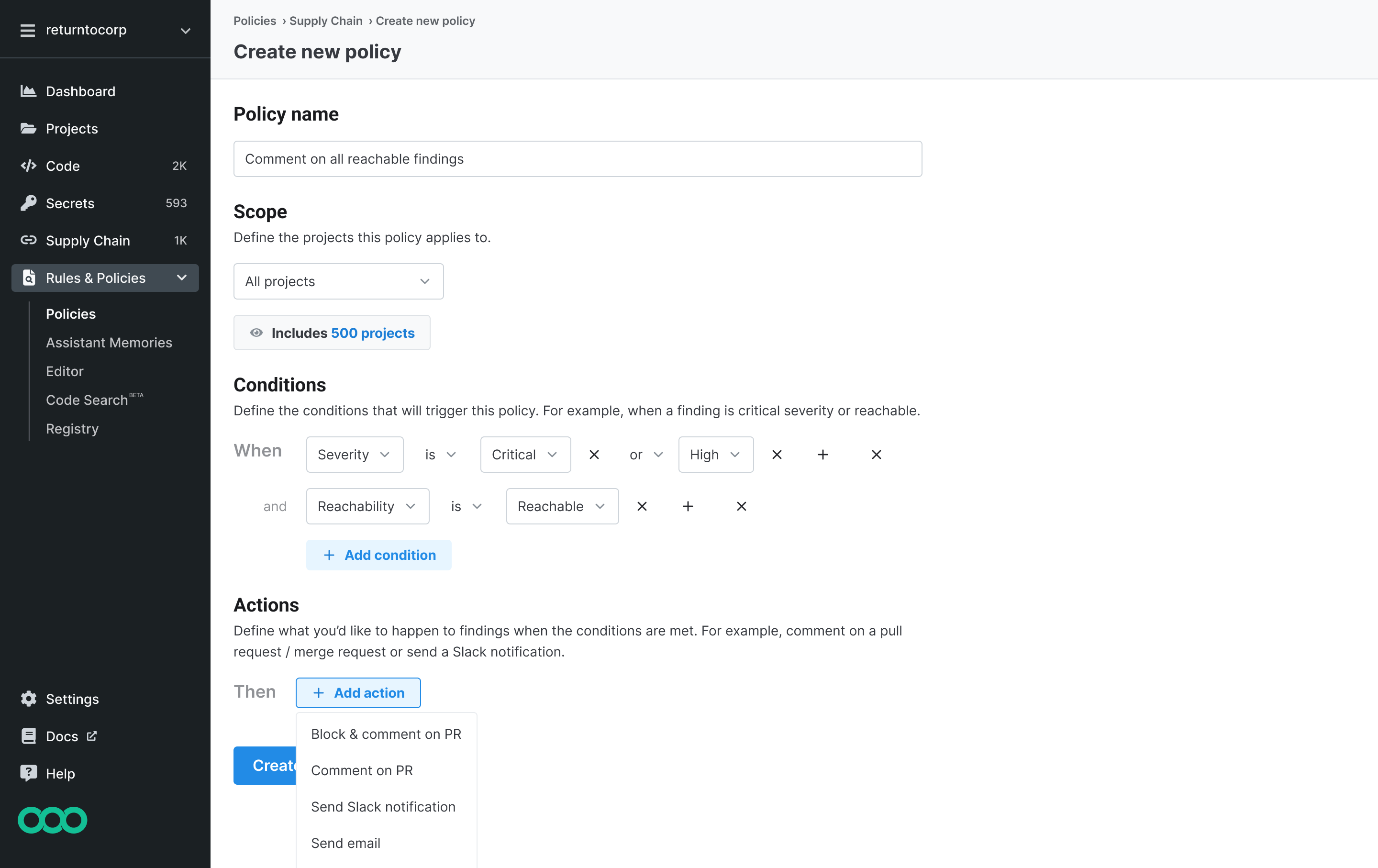
Giving security teams automated control over risk
Designing a flexible policy system that gives security teams granular control over how findings are surfaced to developers
This is just a brief overview of this project. Contact me for a full case study.
Overview
Led the design of customizable supply chain policies that give AppSec teams granular control over how findings are monitored and surfaced to developers, unlocking safer guardrail adoption and strengthening our competitive position.
The problem
Teams lacked meaningful control over how supply chain findings were surfaced to developers. Existing controls were inconsistent with other parts of the platform and difficult to roll out incrementally across repositories. This created friction between AppSec and developers, weakened our secure guardrails story, and put us at a disadvantage against competitors like Snyk, especially in enterprise evaluations.
My role
Design lead, owning problem framing, research, solution definition, and iteration through public beta.
The solution
I designed a flexible, condition-based policy system that allows teams to define how supply chain findings are monitored or enforced based on attributes like reachability, severity, EPSS, and transitivity.
Impact
supply chain policies created since public beta
in ARR supported by the feature
Additional impact:
- No longer a POV loss reason in competitive deals
- Established the foundation for broader automations across the platform
- Defined a multi-quarter roadmap for future policy and automation capabilities